CMC talk addresses challenge of cyber-security and warfare
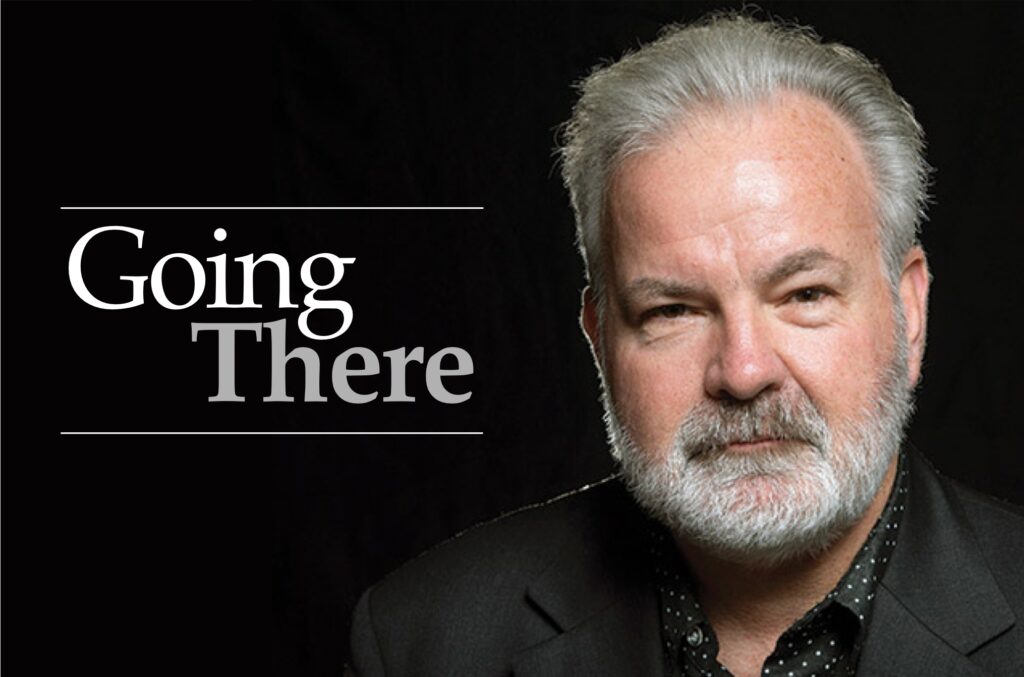
The United States is vulnerable to cyber-attacks of every ilk, from theft to all-out war. This was the message delivered Tuesday evening at Claremont McKenna’s Athenaeum by Richard Clarke, CEO of the Good Harbor Security Risk Management company.
Mr. Clarke, whose talk was called “Cybersecurity in 2015: from Theft to Destruction,” brings a lot of experience to bear on the subject. Among his accomplishments are a decade as a White House official, during which time he counseled three consecutive presidents on national security in the information age.
The ways corporate and governmental security can be breached via computer are myriad, and their execution technical. Mr. Clarke sought to simplify things by breaking down the four main types of digital attacks. They can be remembered via the acronym CHEW, which stands for cyber-crime, cyber-hacktivism, cyber-espionage and cyber-war.
Cyber-crime represents basic theft, in which an individual or individuals reach into peoples’ accounts and remove money, and is a pretty well-known problem. Cyber-hacktivism is when a group, unhappy with the actions of another group, hacks into their system in order to embarrass or sabotage them.
In a way, the Sony Pictures Entertainment Hack, which took place last November, is a case of cyber-hacktivism, according to Mr. Clarke. The North Korean government didn’t want The Interview, a comedy about a plot to assassinate the country’s leader Kim Jong-un, to be released. “Which, having seen the movie, I understand,” Mr. Clarke joked. So the government took action, releasing confidential data about the entertainment giant, including damning personal email exchanges. The fall-out resulted in the firing of Sony co-chair Amy Pascal.
While the problem of cyber-crime is well-known, Mr. Clarke seeks to spread awareness of the staggering cost of cyber-espionage. It is a form of attack in which an individual or individuals reaches into the data systems of a company and uses vital information for personal gain. It is a problem so prevalent that FBI Director Robert Mueller has said, “There are only two types of companies: Those that have been hacked and those that will be.”
In many cases, cyber-espionage is perpetrated by nations bent on economic dominance. China is one of the main culprits, according to Mr. Clarke. The Chinese government regularly eschews costly research and development, instead stealing the intellectual property of US corporations and handing it to Chinese companies.
He cited as an example Cisco Systems, which was once the world’s prime manufacturer of networking equipment. Cisco was hacked by the Chinese government and the next thing you know, a company called Wuwei was offering products eerily similar to those manufactured by Cisco. While Cisco is still the dominant networking company in the United States, Wuwei now dominates the European and Asian markets.
Such brazen digital coups result in the loss of billions of dollars and thousands of jobs each year, Mr. Clarke said. And yet the destructive capabilities of cyber-espionage are trumped by those of cyber-war.
Cyber-war, Mr. Clarke explained, is when computer programming is used to cause physical mayhem. For example, China and Russia have already hacked into the US power grid. Should these countries ever wish to attack the United States, they could act quickly, not just shutting down power temporarily but destroying generators and transistors. It could take months to power back up, Mr. Clarke said, noting that “People don’t just keep extra generators around.”
Cyber-war isn’t just a hypothetical. The first salvos having already been fired. Take a recent exchange between the US and Iranian governments.
In 2010, President Obama ordered a sophisticated cyber-attack against the computer systems running Iran’s nuclear enrichment facilities. The Iranians were using centrifuges to purify uranium, hoping to harvest bomb-grade quantities of the radioactive element. A computer worm called Stuxnet was released, causing the centrifuges to spin in such a way that they exploded. It was a devastating blow to the country’s nuclear program.
The Iranian government responded in 2012 by attacking the largest of United States banks in successive waves. Millions of customers of companies like Wells Fargo and Bank of America found themselves unable to bank online. Iran sent a clear message, Mr. Clarke said: If you mess with us, we will reach into the very heart of your financial system and wreak havoc.
Cyber-security is tricky because it represents what Mr. Clarke calls “offense preference.” It costs thousands of times more money to defend your resources from a digital attack than to perpetrate one. Many companies have sprung up with the goal of providing cyber-security to companies. Their wares, however, constitute little more than Band-Aid measures that can temporarily deter hacking before a workaround is developed.
Another troubling factor is that the skill-sets needed for a cyber-attack are spreading much faster than the analog danger of nuclear proliferation. It begs the question: Will terrorist groups soon be able to launch an all-out cyber-war?
As if the United States needs one more challenge in the area of cyber-security, the government is faced with a tough sales pitch. In light of Edward Snowden’s revelations that the National Security Agency was spying en masse on the activities of US citizens, many Americans mistrust the NSA. And yet, the NSA is the organization that will be utilized in helping to prevent and counter cyber-attacks. In order to receive citizen support, the agency would need to engage in a public relations makeover and “would have to be very transparent in its efforts,” Mr. Clarke said.
Mr. Clarke is a realist, but he is not a pessimist. He sees the coming years not just as a time of threat but also as an era of opportunity. Now is the chance for policy-makers to create new regulations addressing cyber-security. It is an endeavor that will have to be undertaken on an international scale, given the fact that the virtual world knows no boundaries.
We are still using basically the same form of Internet first utilized in the 1980s, he emphasized. Mr. Clarke said it is time for sharp young people like the students at CMC to get to work on new technology, honing new and better ways of encryption and even changing the face of the Internet.
—Sarah Torribio
storribio@claremont-courier.com









0 Comments